GitHub AI agent finds over 80 security flaws in open source code
GitHub's security research team has developed an AI-powered tool that automatically discovers vulnerabilities in software code, leading to more than 80 security issues reported in open source projects so far.
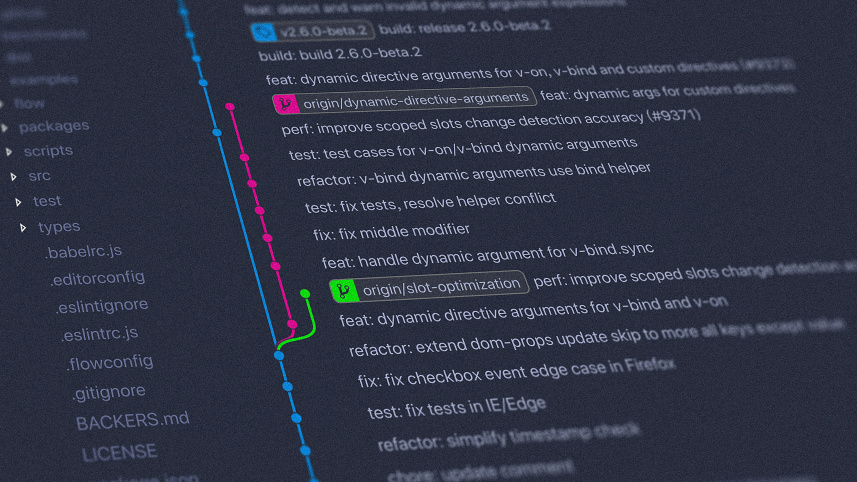
The tool, called the GitHub Security Lab Taskflow Agent, uses large language models to perform structured security audits. It operates by breaking down the auditing process into a series of defined steps, or 'taskflows', rather than relying on a single large prompt.
According to a blog post from the team, approximately 20 of the discovered vulnerabilities have already been publicly disclosed. Many are described as high-impact issues including authorisation bypasses that allow users to log in as someone else or access private data belonging to other users.
The auditing process follows a three-stage approach. First, the agent performs threat modelling by analysing the repository to identify different components, entry points, and intended functionality. Second, it suggests potential vulnerability types that might exist in each component. Third, it rigorously audits those suggestions by examining the actual source code, requiring concrete evidence such as file paths and line numbers.
The team reported that the tool has been particularly effective at finding logic bugs, including access control issues, which traditional security tools often miss. In one example, the agent discovered a privilege escalation vulnerability in the collaborative web application Outline, where low-privileged users could grant themselves admin permissions on documents.
In another case, the tool found multiple flaws in ecommerce platforms including WooCommerce and Spree, allowing unauthorised access to customer addresses and personal information from shopping carts. A critical vulnerability was also discovered in Rocket.Chat, where the agent identified that users could log in as anyone using any password due to a missing code that properly handled password validation.
The team noted that out of 1,003 suggested issues across more than 40 repositories, 139 were marked as potential vulnerabilities. After manual inspection, 19 were considered impactful enough to report, with the majority having high or critical severity.
The taskflows are open source and available for others to use on their own projects, though a GitHub Copilot license is required. The team encouraged others to contribute to the framework.


 For all latest news, follow The Daily Star's Google News channel.
For all latest news, follow The Daily Star's Google News channel.
Comments